Our automated scanners identify all exposed assets domains, IPs, subdomains, and cloud instances providing a real-time inventory of your digital footprint. This ensures no asset remains unmonitored or vulnerable.
- Visual scan
- AI supported crawler
We continuously map your external attack surface, monitoring DNS/SSL, open ports, and vulnerabilities in real time. Gain complete visibility of your infrastructure and strengthen resilience against cyberattacks.
Our automated scanners identify all exposed assets domains, IPs, subdomains, and cloud instances providing a real-time inventory of your digital footprint. This ensures no asset remains unmonitored or vulnerable.
We identify security misconfigurations, outdated software, and exploitable weaknesses across your infrastructure. ach issue is categorized by risk level, helping you focus on the most critical vulnerabilities first.
Gain centralized visibility of all external assets with detailed dashboards and automated reports.
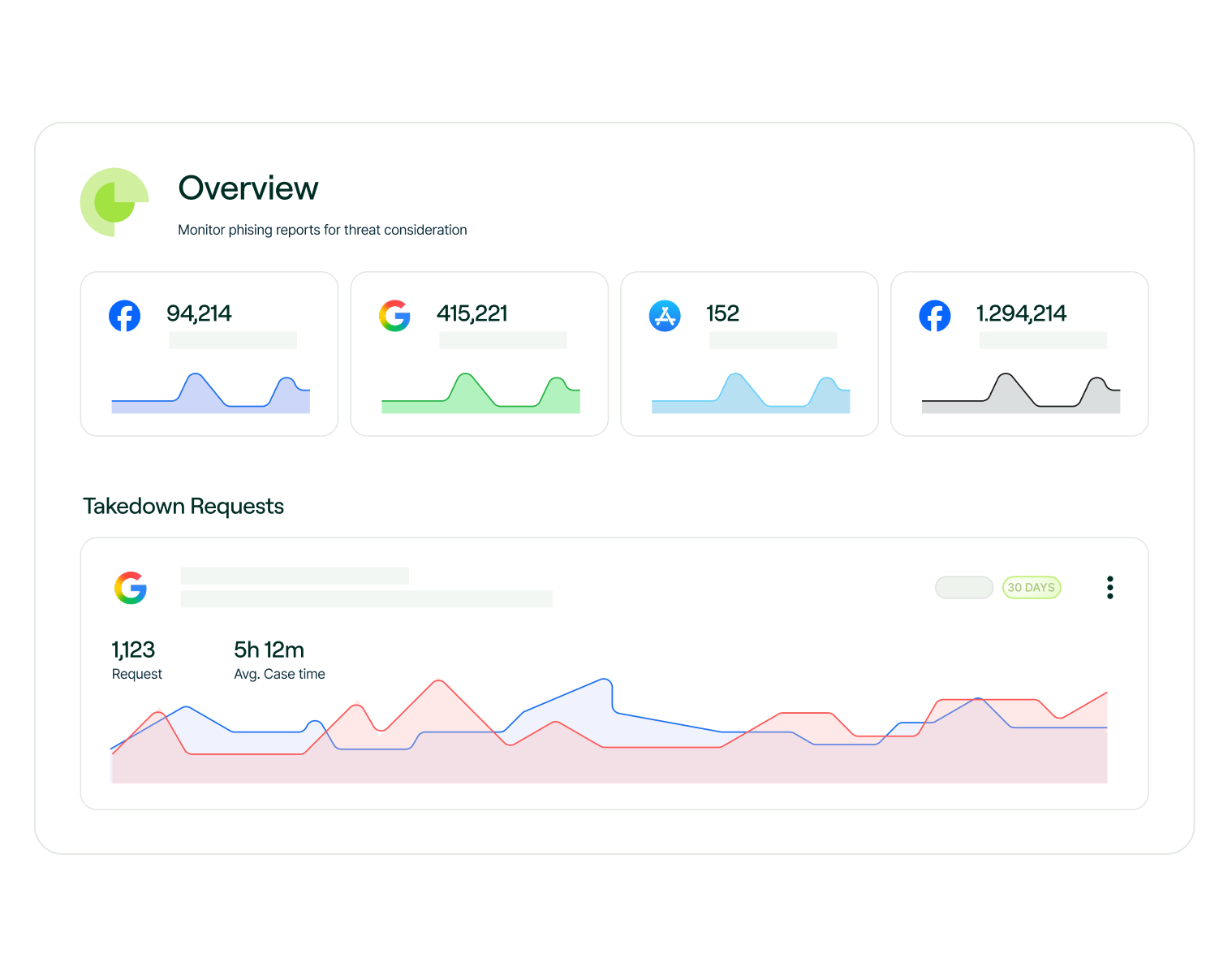
Our system continuously monitors your DNS, SSL certificates, and exposed ports, detecting suspicious changes instantly. Receive alerts before attackers exploit vulnerabilities.
It identifies exposed assets and supports Exposure Management and Cyber Risk Management.
It uses DNS Monitoring, SSL Security, and Network Scanning to detect threats.
It finds weaknesses in systems to improve Cyber Resilience.
It detects outside risks early and reduces exposure.
They detect issues and strengthen Infrastructure Protection.