According to recent findings obtained within the scope of cyber threat intelligence, a significant increase has been observed in "device code phishing" attacks that abuse the OAuth 2.0 Device Authorization Grant flow as of 2026. This attack technique poses a high risk because it enables the direct acquisition of valid access and refresh tokens without compromising user credentials and has the potential to bypass existing security controls. This increase indicates that the attack technique has become more widespread and can reach more targets.
Analysis of the Attack Technique
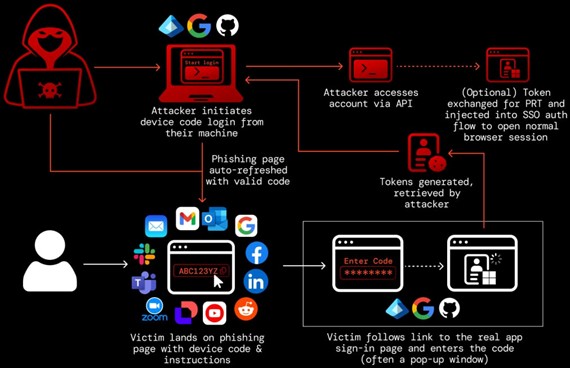
In this attack technique, threat actors generate a device code through legitimate services and deliver this code to the target user using various social engineering methods. By persuading the user to enter this code on official login pages, the attacker’s device can gain access authorization to the user’s account. During this process, the user often believes they are performing a normal operation.
Unlike traditional phishing attacks, this method does not directly target credentials such as usernames and passwords; instead, it exploits legitimate authentication flows to obtain valid access and refresh tokens, which may allow attackers to maintain long-term access.
Current Threat Assessment
Recent analyses indicate that the use of this attack technique has increased by more than 37 times compared to the beginning of the year, and it has become accessible to a wider range of threat actors, especially through Phishing-as-a-Service (PhaaS) platforms. This situation points to an expanded threat surface. This increase shows that attacks have become more accessible through automation and service-based models.
The following themes are predominantly used in the attacks:
- Microsoft 365 enterprise services
- Document sharing platforms (SharePoint, OneDrive, Google Drive)
- Enterprise SaaS services and collaboration tools (Slack, Zoom, Teams)
Recommended Security Controls
In this context, it is recommended that organizations urgently review the following controls:
- Restricting the Device Authorization Flow: The use of the Device Authorization Grant flow should be limited when not necessary or considered for complete disablement.
- Monitoring Authentication Logs: Authentication logs should be proactively monitored, especially for device code-based login attempts.
- Anomaly Detection: It is recommended to strengthen mechanisms for detecting abnormal IP addresses, session behaviors, and token-based access activities.
- User Awareness: Conducting awareness and training activities to increase user awareness is of critical importance, and the level of awareness in this area should be improved.
Assessment and Conclusion
These activities clearly demonstrate that attack techniques targeting the identity and access management (IAM) layer are becoming increasingly widespread and that threat actors are shifting toward exploiting legitimate authentication flows, indicating a change in their approach. In particular, the development of the PhaaS ecosystem enables even low-skilled threat actors to use such sophisticated attack techniques, leading to a wider spread of these attacks.
It is of critical importance for organizations to strengthen controls against token-based access exploitation, beyond traditional defense mechanisms focused on credential theft, and to increase awareness in this area.
MITRE ATT&CK Mapping
| Tactic | Technique ID | Technique Name |
| Initial Access | T1566.002 | Phishing: Spearphishing Link |
| Credential Access | T1528 | Steal Application Access Token |
| Defense Evasion | T1550.001 | Use Alternate Auth Material |

